Who this is for
This article is for product, commercial and data teams at GRC platforms evaluating how to expand framework coverage without increasing manual regulatory data work.
The pressure on GRC platforms is changing
GRC platforms are being asked to do more.
More frameworks. More jurisdictional variants. More evidence behind the controls their clients rely on. More ability to show how an internal control relates to external regulatory requirements, and where in the source text that requirement comes from.
This pressure is not abstract. DORA is live. NIS2 has landed unevenly across EU member states. NIST CSF 2.0 has changed the shape of cyber framework conversations. ISO 27001 has required firms to revisit existing mappings. Newer areas, including AI governance and operational resilience, are creating demand for control models that are still taking shape.
For GRC platforms, this creates a very specific challenge. The product roadmap may be ready to support more frameworks and more client use cases, but the regulatory data layer underneath the platform often is not.
Framework expansion is becoming a data layer problem.
Framework expansion is not just a product task
From the outside, adding a new framework can look like a product configuration exercise. In practice, it is much more involved.
Before a framework can be used inside a GRC platform, the underlying regulatory and control content needs to be identified, reviewed, structured and connected. Relevant authoritative sources need to be selected. Obligations and control references need to be extracted. Framework relationships need to be preserved. Controls need to be linked back to the source text that supports them. Updates need to be monitored and maintained as regulation and frameworks evolve.
This work sits below the user interface, but it shapes what the platform can credibly deliver.
Without the right regulatory data layer, every new framework becomes a separate manual build. Every local variant requires new expertise. Every client request creates another sourcing, mapping and maintenance exercise.
The platform may be scalable. The data operation underneath it may not be.
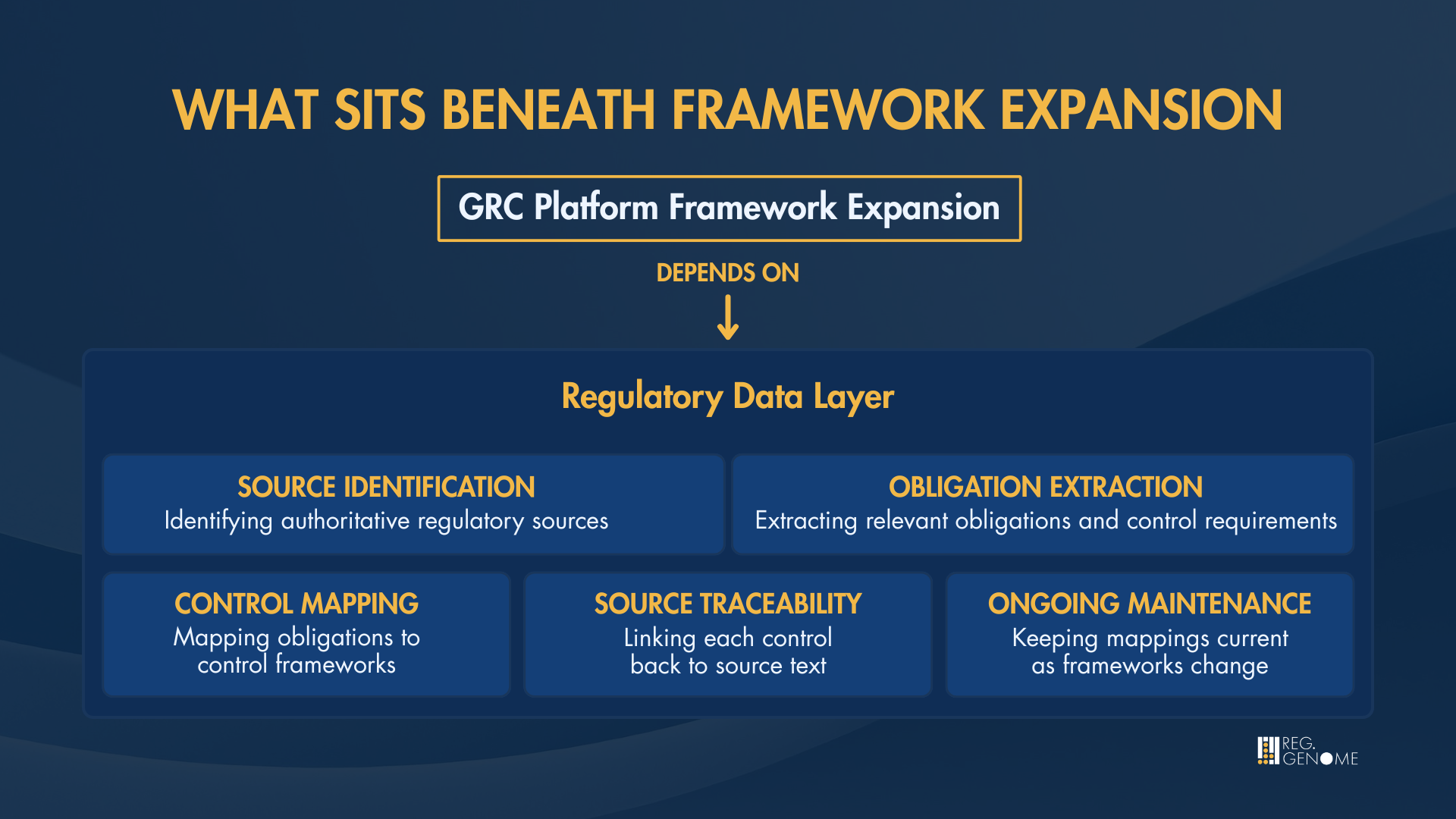
Structured, source-linked data reduces the manual effort required to turn regulatory sources into usable framework coverage.
Why manual construction becomes a growth constraint
Many GRC providers still rely on internal experts, external consultants, spreadsheets, client-supplied inputs or generic content sources to build and maintain framework coverage.
That approach can work for a limited number of established frameworks. It becomes harder when the platform needs to support more jurisdictions, more local regulatory requirements, or new cyber and operational resilience themes where common control models are still maturing.
Manual framework construction creates four constraints.
First, it slows expansion. Each new framework or local variant requires time to source, analyse, structure and validate.
Second, it depends on specialist expertise that may not be available in every market or regulatory domain.
Third, it creates maintenance overhead. Frameworks change, regulation evolves, and mappings need to be reviewed over time.
Fourth, it can be difficult to audit. Expert-built controls may be reasonable, but if they cannot be traced back to a specific regulatory source, legal and audit teams have limited evidence to work with.
For GRC platforms, this becomes a growth ceiling. The ability to serve more clients, in more markets, depends on how quickly and confidently the platform can expand the data layer beneath its workflows.
Why source-linked data matters
A control in a GRC platform is not the end of the chain. For many stakeholders, it is the start of the next question.
- Where did this control come from?
- Which regulatory obligation does it support?
- Which source text backs it up?
- Has that source changed?
- Can legal or audit verify the connection?
Risk and compliance teams may be comfortable working at the framework level. Legal teams often need to review the authoritative text. Internal audit needs to understand whether the controls in the platform are grounded in current, traceable requirements, not just inferred from internal judgement.
This is where source-linked data becomes critical.
When each control and obligation links back to authoritative regulatory source text, the platform can support a clearer evidence trail. It can help users understand not only that a control exists, but why it exists and which regulatory requirement it helps address.
That traceability is increasingly important as GRC platforms move deeper into client workflows. The more a platform supports control mapping, gap analysis, regulatory change and audit preparation, the more the quality of the underlying data matters.
What structured control and obligation data enables
Structured control and obligation data gives GRC platforms a stronger foundation for framework expansion.
It allows platforms to ingest control and obligation data in a machine-readable format. It preserves framework relationships and document hierarchy. It links controls and obligations back to source regulation. It supports alignment across overlapping frameworks, helping platforms show where controls satisfy more than one requirement.
For cyber GRC platforms, control mapping regulatory data is becoming part of the product infrastructure. It determines how quickly new frameworks can be added, how clearly controls can be evidenced and how confidently platforms can respond to client demand.
For product teams, this reduces the amount of manual content work needed before a framework can become usable inside the platform.
For commercial teams, it supports faster response to client demand, especially where customers are asking for new frameworks, local variants or clearer source traceability.
For end users, it provides more reliable evidence behind the controls they rely on.
For legal and audit stakeholders, it creates a clearer path back to the source text.
The result is not simply faster framework onboarding. It is a more scalable way to support the control workflows GRC platforms are already being asked to deliver.
What this means for GRC platform teams
For GRC platforms, framework expansion is no longer only a question of product ambition. It is a question of whether the data layer underneath the platform can support the pace, precision and traceability clients now expect.
For product teams
Framework expansion becomes easier to prioritise because the underlying control and obligation data is already structured for platform use.
For data and technical teams
The data can be evaluated for ingestion, source linkage, framework relationships and maintenance requirements.
For commercial teams
The platform can respond more confidently to client demand for additional frameworks, jurisdictions and traceable coverage.
For client-facing teams
Source-linked controls provide a clearer way to explain how framework coverage is built, maintained and evidenced.
From framework coverage to data infrastructure
The next phase of GRC will not be defined only by which platforms have the longest list of supported frameworks.
It will be defined by how well those platforms can maintain, map and evidence those frameworks as regulation changes.
That requires a regulatory data layer designed for product integration, not a static content layer that has to be reconstructed internally.
Controls Library provides structured, source-linked control and obligation data mapped to key frameworks and built for GRC platform integration. It is designed to help GRC providers reduce manual framework work, support clearer traceability and expand coverage with greater confidence.
Ready to see how the data works inside your platform?
Request a data sample and we will walk you through the structure, coverage and source linkage.
Test the data in your own environment.